
Playbook for the Secure Enterprise
CyberSecurity Latest Rundown
Heroes, here's info your security rundown for Jan 15, 2026.
 CRITICAL ITEMS
CRITICAL ITEMS
-
Palo Alto Fixes GlobalProtect DoS Flaw That Can Crash Firewalls Without Login
Date & Time: 2026-01-15T08:18:00
Palo Alto Networks has patched a high-severity vulnerability in GlobalProtect Gateway and Portal that allows unauthenticated attackers to crash the service. A proof-of-concept exploit exists, making immediate exploitation highly likely for exposed interfaces.
Business impactA successful attack results in a Denial of Service (DoS), severing VPN access for remote employees and potentially disrupting business continuity. While data theft is not the primary risk, operational downtime for remote workforces could be significant.Recommended actionAsk your IT team: "Have we applied the latest PAN-OS updates to our GlobalProtect Gateways, specifically addressing CVE-2026-0227?"CVE: CVE-2026-0227 | Compliance: SOX | Source: The Hacker News ↗ ↗
 HIGH SEVERITY ITEMS
HIGH SEVERITY ITEMS

-
A single click mounted a covert, multistage attack against Copilot
Date & Time: 2026-01-14T22:03:11
Researchers discovered a vulnerability in Microsoft Copilot where a single click on a malicious URL could allow attackers to exfiltrate sensitive user data managed by the AI assistant. The attack leverages the AI's excessive permissions to access and summarize private emails and documents for the attacker.
Business impactThis exposes organizations to massive data leakage of intellectual property and internal communications. If an executive clicks a lure, the AI could inadvertently package and send confidential strategy documents to an external adversary.Recommended actionVerify with your security team: "Do we have Data Security Posture Management (DSPM) controls in place to limit what data Copilot can access, and has the Microsoft fix been verified in our tenant?"CVE: n/a | Compliance: SOX | Source: Ars Technica ↗ ↗
-
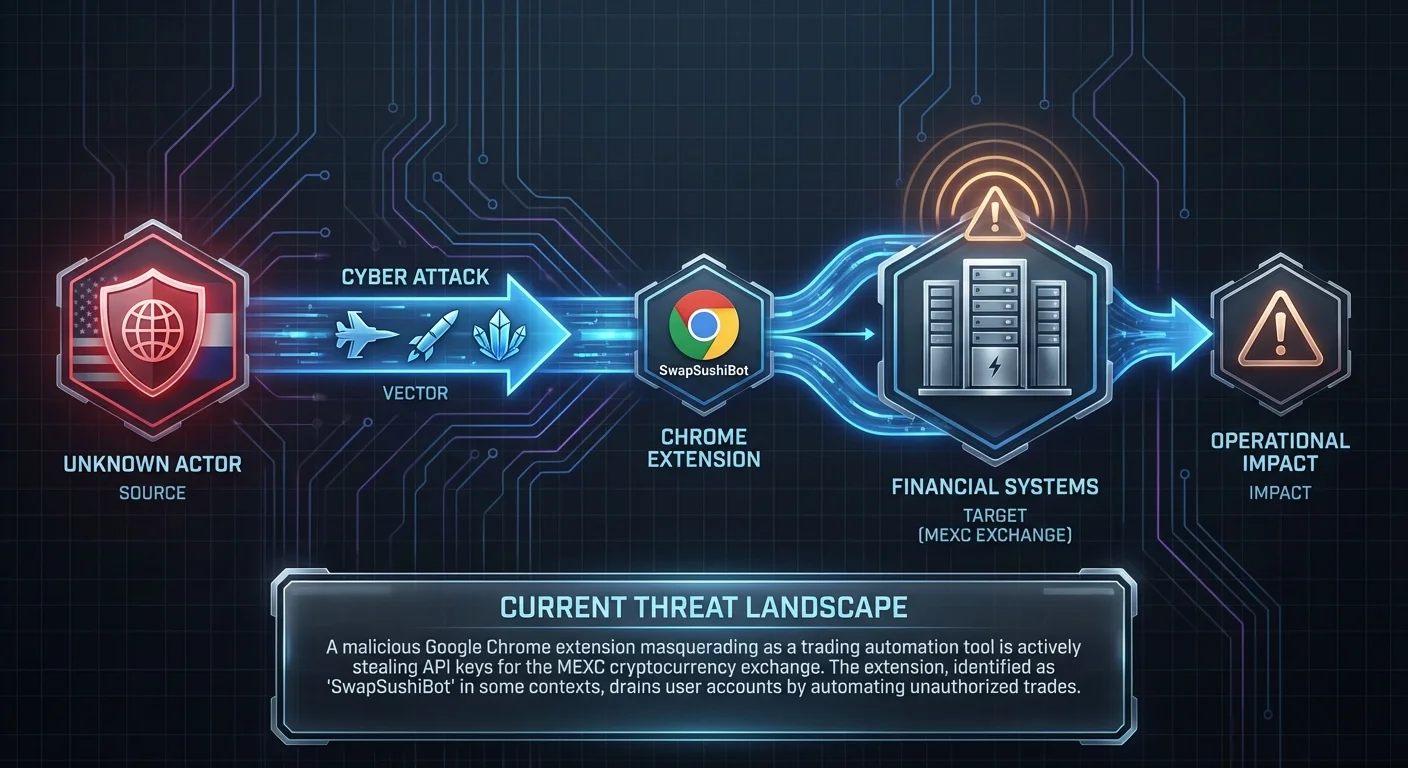
Malicious Chrome Extension Steals MEXC API Keys
Date & Time: 2026-01-14T07:23:27
A malicious Google Chrome extension masquerading as a trading automation tool is actively stealing API keys for the MEXC cryptocurrency exchange. The extension, identified as "SwapSushiBot" in some contexts, drains user accounts by automating unauthorized trades.
Business impactFor financial organizations or employees managing corporate crypto assets, this represents a direct financial loss risk. It also highlights the danger of unmanaged browser extensions in the enterprise environment.Recommended actionAsk IT: "Do we enforce a blocklist for browser extensions, and can we scan endpoints for the presence of unauthorized trading tools?"CVE: n/a | Compliance: SOX | Source: Lifeboat ↗ ↗
OTHER NOTEWORTHY ITEMS
-
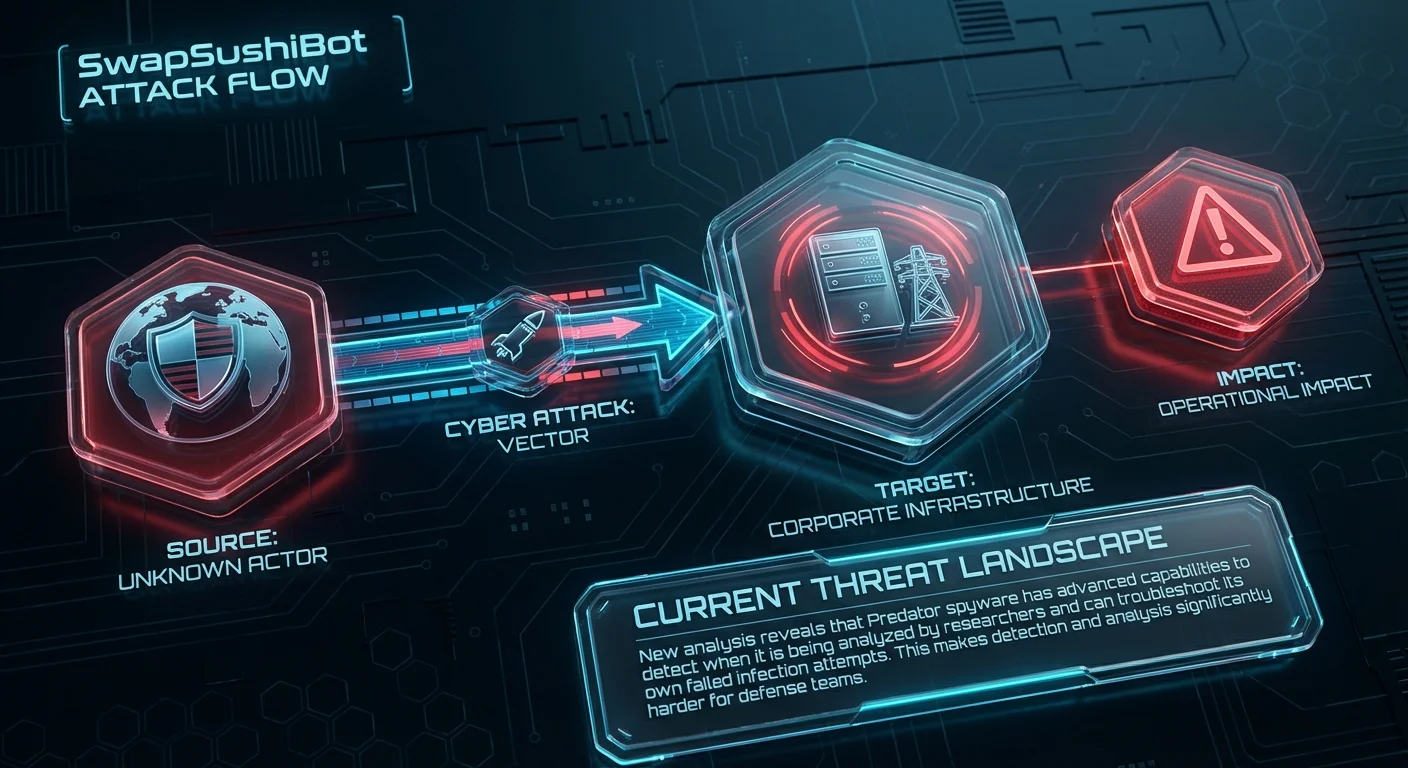
Predator spyware demonstrates troubleshooting, researcher-dodging capabilities
Date & Time: 2026-01-14T18:16:49
New analysis reveals that Predator spyware has advanced capabilities to detect when it is being analyzed by researchers and can troubleshoot its own failed infection attempts. This makes detection and analysis significantly harder for defense teams.
Business impactHigh-value targets (executives, R&D leads) are at increased risk of undetectable mobile espionage. Compromise could lead to the theft of sensitive conversations, location data, and trade secrets without the victim's knowledge.Recommended actionReview mobile device management (MDM) policies for executive devices and consider specialized mobile threat defense solutions for high-risk personnel.CVE: n/a | Compliance: SOX | Source: CyberScoop ↗ ↗
 VENDOR SPOTLIGHT
VENDOR SPOTLIGHT
-
Menlo Security
Specialization: Browser Security and Secure Access Service Edge (SASE)
Why Menlo Security Today: Menlo Security is directly relevant to the threat involving the malicious Chrome extension, as their browser security platform specifically detects and blocks malicious extensions and prevents credential theft. Furthermore, their Remote Browser Isolation (RBI) technology neutralizes risks associated with clicking malicious URLs, such as the vector described in the Microsoft Copilot attack.
Key Capability: Remote Browser Isolation (RBI) to neutralize browser-based threats and extension risks
Recommended Actions: 1. Navigate to Menlo Security Admin Console → Policy → Browser Security → Extension Policy 2. Navigate to Menlo Security Admin Console → Policy → Web Policy → Security 3. Navigate to Menlo Security Admin Console → Policy → Web Policy → Content & File Controls → Input Controls
Verification Steps: - Attempt to install a test extension not on the Allow List or visit a site hosting the blocked extension ID - Navigate to a test site categorized as 'Uncategorized' (or use safe.menlosecurity.com/isolate)
This guidance assumes the standard Menlo Security Isolation Platform (MSIP) interface. UI paths may vary slightly depending on whether the tenant is configured for the classic view or the new dashboard (HEAT Shield integration).
 DETECTION & RESPONSE KIT
DETECTION & RESPONSE KIT
-
⚠️ Disclaimer: Test all detection logic in non-production environments before deployment.
1. Vendor Platform Configuration - Menlo Security
2. YARA Rule for Malicious Chrome Extension (MEXC Stealer)
rule Browser_Extension_SwapSushiBot_MEXC { meta: description = "Detects artifacts related to the malicious SwapSushiBot Chrome extension targeting MEXC API keys" author = "Threat Rundown" date = "2026-01-15" reference = "https://lifeboat.com/blog/2026/01/malicious-chrome-extension-steals-mexc-api-keys-by-masquerading-as-trading-tool" severity = "high" tlp = "white" strings: $s1 = "SwapSushiBot" ascii wide $s2 = "MEXC" ascii wide $s3 = "api_key" ascii wide $s4 = "trading_tool" ascii wide condition: $s1 and ($s2 or $s3 or $s4) }3. SIEM Query — RedVDS/Storm Infrastructure Traffic
index=security sourcetype="firewall" OR sourcetype="web_proxy" (dest_host="*redvds*" OR dest_host="*storm*" OR user_agent="*RedVDS*") | eval risk_score=case( like(dest_host, "%redvds%"), 100, like(user_agent, "%RedVDS%"), 100, 1==1, 25) | where risk_score >= 50 | table _time, src_ip, dest_ip, dest_host, user_agent, risk_score | sort -_time4. PowerShell Script — Check for GlobalProtect Version (CVE-2026-0227)
This rundown should provide a solid overview of the current threat landscape. Thank you to all our cyberheroes for your diligence and hard work. Stay vigilant!

